In an era defined by data breaches, sophisticated cyber-attacks, and the looming threat to digital encryption, a silent revolution is unfolding in the laboratories of physicists and engineers. The recent achievement of the world’s first truly secure transmission over a prototype quantum internet is not merely a scientific milestone; it is the foundational stone for a future internet impervious to conventional hacking. This breakthrough transcends incremental technological advancement it represents a paradigm shift in how we conceive information security, data sovereignty, and global connectivity. While the classical internet shuffles bits (0s and 1s), the quantum internet harnesses the bizarre, non-intuitive laws of quantum mechanics to create a network where information is protected by the fundamental laws of physics. This article delves deep into the mechanics, profound implications, formidable challenges, and the exhilarating roadmap of this technology that promises to redefine security in the digital age.
Deconstructing the Core: Quantum Entanglement and Superposition
To grasp the magnitude of this achievement, one must first understand the two quantum phenomena that make it possible: Superposition and Entanglement.
A. Superposition: Unlike a classical bit, which is definitively either 0 or 1, a quantum bit, or qubit, can exist in a state of superposition simultaneously representing 0 and 1. Imagine a spinning coin suspended in mid-air; it is neither purely heads nor purely tails until observed. This ability to hold multiple states at once grants quantum systems immense computational and communicative power.
B. Quantum Entanglement: This is the heart of the quantum internet. When two qubits become entangled, they forge a profound connection. Their quantum states are linked inextricably, regardless of the physical distance separating them—be it across a lab bench or across a galaxy. Measuring the state of one entangled qubit instantaneously determines the state of its partner. This “spooky action at a distance,” as Einstein famously called it, is the un-hackable channel for quantum communication.
The Breakthrough: How the First Secure Transmission Actually Worked
The historic secure transmission leveraged a process known as Quantum Key Distribution (QKD). It’s crucial to note that QKD does not send the actual message data through quantum channels. Instead, it uses quantum mechanics to generate and share an ultra-secure random encryption key.
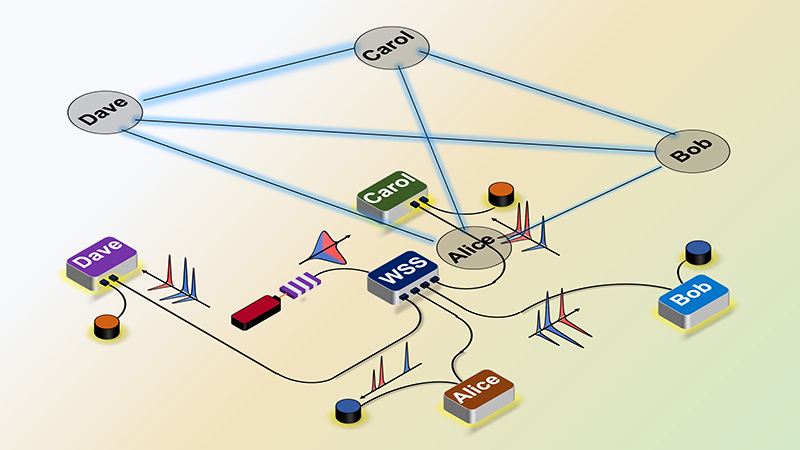
A. The Setup: The experiment typically involved two separate quantum nodes (Node A and Node B), often housed in different buildings or cities, connected by a special optical fiber link designed for delicate quantum states.
B. Generating Entanglement: A central source, or sometimes one of the nodes, generated a pair of entangled photons (light particles). These photons were then dispatched, one to Node A and the other to Node B.
C. The Quantum Measurement: Upon receiving their respective entangled photons, both nodes independently and randomly measured their qubits’ properties (e.g., polarization). Due to entanglement, their measurement results, while random individually, were perfectly correlated. This correlation is the raw material for the secret key.
D. Sifting and Creating the Key: Subsequently, Nodes A and B communicate over a classical public channel (the regular internet) to compare which measurement bases they used, not the results. They discard all measurements where they used mismatched bases. The remaining, correlated results are translated into a string of identical, truly random bits the secret cryptographic key.
E. The “Unbreakable” Security: This security arises from the quantum no-cloning theorem and the nature of measurement. Any eavesdropper (Eve) attempting to intercept a quantum photon to read its state must measure it. This measurement inevitably disturbs the fragile quantum state. Legitimate users (Alice and Bob) can detect this disturbance by noting an anomalously high error rate in their correlated keys. They can then discard the compromised key. Thus, security is not based on computational difficulty (which advancing computers can break), but on a law of physics.
Profound Implications: A World Transformed by Quantum Security
The maturation of a global quantum internet will catalyze transformations across every sector of society.
A. Ultra-Secure Communications: Governments and military organizations could communicate with guaranteed confidentiality. Diplomatic cables, strategic defense data, and intelligence sharing would enter a new realm of security.
B. Financial Sector Revolution: Bank-to-bank transactions, stock exchange orders, and personal banking data could be shielded from even the most powerful quantum computer attacks, preventing fraud worth billions.
C. Healthcare and Privacy: The secure transmission of sensitive patient records, genomic data, and medical research between institutions would protect individual privacy while accelerating collaborative breakthroughs.
D. Critical Infrastructure Protection: Power grids, water supply systems, and air traffic control networks, which are increasingly targeted by cyber-warfare, could be managed through control channels secured by quantum cryptography.
E. The Future of Digital Identity: Quantum-secure digital signatures could create unforgeable personal identities, potentially eliminating identity theft and securing everything from online voting to property deeds.
F. Connecting Quantum Computers: Perhaps the most transformative long-term implication is the creation of a “quantum cloud.” Just as today’s cloud connects classical computers, a quantum internet would link quantum processors, amplifying their power exponentially to solve problems in drug discovery, materials science, and climate modeling that are currently intractable.
The Daunting Challenges on the Path to a Quantum Web
Despite the exciting breakthrough, the road to a global quantum internet is paved with significant scientific and engineering hurdles.
A. Distance Limitation and Loss: Quantum states, especially entangled photons, are incredibly fragile. They can be absorbed or scattered in optical fibers, limiting transmission distances to a few hundred kilometers before signal loss is complete. This is known as channel loss.
B. Quantum Repeaters: The solution to the distance problem lies in quantum repeaters. Unlike classical repeaters that amplify a signal, quantum repeaters must create a chain of entangled pairs and perform a complex process called entanglement swapping to extend the secure link across continents without destroying the quantum state. Developing reliable, fast quantum repeaters is the single most critical engineering challenge.
C. Matter Qubit Stability: While photons are ideal for transmitting quantum information, they are hard to store. For processing and memory, matter qubits (using trapped ions, superconducting circuits, or silicon vacancies) are needed. These qubits are notoriously error-prone and decohere (lose their quantum state) quickly. Error correction codes for quantum networks are vastly more complex than classical ones.
D. Integration with Classical Infrastructure: The quantum internet will not replace the classical internet but will overlay and integrate with it. Developing standardized protocols, interfaces, and hybrid network architectures is a massive undertaking requiring global cooperation.
E. Cost and Scalability: Current quantum networking equipment is laboratory-grade, expensive, and requires extreme environmental control. Making this technology scalable, affordable, and operable outside a lab is essential for widespread adoption.
The Global Race: Who is Leading the Charge?
The development of the quantum internet is a key front in global technological competition, with significant players making strides.
A. The United States: Led by the Department of Energy, a national laboratory network is building a quantum internet testbed. Key institutions like Caltech, Fermilab, and others have successfully demonstrated multi-node entanglement.
B. China: Has made massive investments, claiming world records for ground-based QKD distances and demonstrating satellite-based QKD (“Micius”) on an intercontinental scale, a formidable approach to bypassing terrestrial fiber limitations.
C. The European Union: The EU’s Quantum Internet Alliance is coordinating efforts across member states, focusing on creating a functional quantum web ecosystem across Europe, with strong contributions from the Netherlands (QuTech) and others.
D. Private Sector: Companies like Google, IBM, Microsoft, and numerous startups (e.g., Quantum Xchange, Toshiba) are heavily invested in developing both the hardware and software layers for future quantum networks, sensing a vast commercial opportunity.
Looking Ahead: The Quantum Internet Roadmap
Experts envision a staged evolution over the coming decades:
-
Present – 2025: The “Trusted Node” Network. Secure point-to-point links for high-value applications, with trusted intermediate nodes.
-
2025 – 2035: The “Quantum Repeater” Network. The first true quantum internet emerges as entanglement is extended over cities and countries using initial quantum repeater technology.
-
2035 – 2050: The “Quantum Memory” Network. A fully functional, long-distance network incorporating quantum memory for advanced applications like distributed quantum computing and secure quantum cloud services.
-
2050+: The “Global Quantum Web.” A seamless, planet-scale integration of terrestrial and satellite quantum links, forming the backbone of global security and an engine for scientific discovery.
Conclusion: Securing Tomorrow, Today

The first secure quantum internet transmission is a beacon, illuminating a path toward a future where our most vital communications are guarded by the immutable laws of physics. While significant challenges remain, the collaborative efforts of global research initiatives and private enterprises are accelerating progress at a breathtaking pace. This is more than a technological upgrade; it is a necessary evolution to safeguard our digital civilization against threats both present and unforeseen. The quantum internet promises not just unbreakable security, but also a new frontier for computation and discovery, heralding the next chapter in the human story of connection. For content creators, technologists, and forward-thinkers, understanding this shift is no longer optional it is imperative to navigating and shaping the digital landscape of tomorrow.







